Fast account opening
in 3 simple steps
Register
Choose your account: 'Standard' for beginners, 'Raw' for experienced traders.
Fund your account
Easily fund your account, with no deposit fees.
Trade
Trade Bitcoin and 10,000 other financial instruments.
Buy or sell Bitcoin in one click
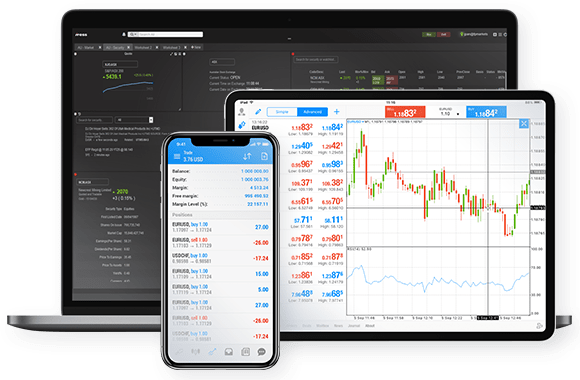
Trade directly from the charts, on your phone or your computer. Click 'Buy' if you expect Bitcoin's price to rise, or 'Sell' if you expect it to fall.
FP Markets offers MetaTrader 4/5, cTrader and TradingView, 4 powerful trading platforms. You can also trade through your browser, with no download required, if you prefer.
Open an account with FP Markets to download any of these platforms free of charge.
Easily fund your FP Markets account

FP Markets accepts a wide range of payment methods and currencies, and charges no fees on deposits.
Fund your account instantly with Visa or Mastercard, Apple Pay or Google Pay, Skrill, Neteller or cryptocurrency.
You can also fund your account through a bank transfer. FP Markets will cover paymentfp fees up to USD 50 when you deposit over USD 10,000.



